Keep (KEEP) Review – Ethereum’s First Private Computer
| Coin Name | Keep |
| Coin Ticker | KEEP |
| Token Type | ERC20 |
| Total Tokens | 1,000,000 |
| Website URL | https://keep.network/ |
| White Paper URL | https://backend.keep.network/whitepaper |
Keep’s goal is to provide a secure multiparty computation (sMPC) that allows generation, security, storing, encrypting and transmitting data across many individuals on the public Ethereum blockchain. In other words, it provides a privacy layer for Ethereum, allowing for the transfer of information on the blockchain that is private even to itself.
Article Summary
- The Idea and the Team Behind Keep
- The Keep Technology
- The Keep Tokens
- The Keep Network
- The ICO and Roadmap
The Idea and the Team Behind Keep
Although public blockchains have brought more transparency and auditability to the financial world than ever before, they have also brought challenges of privacy. At this point, sharing and ensuring the privacy of information such as a credit score in order to assess a borrower’s risk for a loan (information a borrower might want to only reveal to relevant parties) is extremely difficult on the current public blockchain system. The challenge of privacy is not a new concept for the developers of Bitcoin and Ethereum.
“When I and others talk to companies about building their applications on a blockchain, two primary issues always come up: scalability and privacy,” the founder of Ethereum, Vitaly Buterin, has written on the Ethereum blog.
The Keep team includes Matt Luongo and Corbin Pon, both co-founders of Fold, a project aimed at getting people to spend bitcoin in the real world. The two have started several companies together. Matt’s experience lies in technical ability, with many years of experience in crypto, while Corbin’s experience is in the defense industry.
Keep’s fundamental principle is that you should have the ability to control your own data, and idea that is especially pertinent in an era of security attacks such as Equifax, Home Depot and Target. It is different than Nucypher in that it focuses on private computation rather than file sharing. Enigma has a similar privacy protocol as well, but it suffers from Sybil risks like other multi-party computation (MPC) systems.
The Keep team has partnerships with Lendroid, an open protocol enabling decentralized lending and trading and District0x, a network of decentralized markets and communities. Both work on the Ethereum network.
The Keep Technology
Keep’s technology addresses the challenge of building a publicly verifiable, decentralized, censorship-resistant application that enables the transfer of private data. Keep works secure and manipulate private data off-chain but works with smart contracts that are on-chain.
Before Keep, there were a few ways to transmit private data on the blockchain, each with its own advantages and disadvantages:
- Hash-reveal – Contracts that can receive and manipulate hashes of private data, also known as commitments. Users first reveal the private data off-chain before putting it in on-chain. The disadvantage is that users must be online to transmit and receive private data when necessary and validate hashes.
- Private blockchain – Private blockchains are also known as permissioned ledgers and permit. Examples are JP Morgan’s Quorum and Microsoft’s Colo Framework. The disadvantages of a private blockchain are that they aren’t public, don’t provide accountability, aren’t censorship-resistant, and aren’t trustless.
- Zero-knowledge proofs – Proofs that verify strangers with difficult questions that only the stranger with the identity can answer. For example, say someone wants to prove he has access to private information without revealing information linked in any way to the private information. Instead, the person proves his identity and ability to access a private key by encrypting a particular message. The private key (or secret) remains private. However, zero-knowledge proofs still don’t allow direct transfer of the private data and also require participants to be online.
Keeps, or off-chain containers for private data, are the new solution to this challenge. Keeps bring private storage and computation to the public blockchain via Ethereum contracts without risk from a third party.
This is accomplished in three major ways:
- Cryptography – through secure multi-party computation (sMPC), a process where several participants are given a secret and the secret must be reassembled via computation by each participant to reveal it. This can be done without revealing the secret to any of the participants.
- Incentives — participants in the network are given incentives to keep secrets and punish them for misbehavior (such as sharing the secrets).
Unpredictability – Participants in the network are matched up at random to ensure no one can target specific secrets. This is done using Key’s Random Beacon technology.
The real-world applications of Keep will impact the world of finance, healthcare, and business among many others. For example, Keep will allow a Dead Man Switch, a device that automatically activates trust and estate plan in the event that the owner of a will is incapacitated.
The Keep Tokens
Keep tokens are also known as “work tokens.” They are different than tokens used as payment in a network in that you must prove and lock up holdings (otherwise known as “staking”) to participate in the network. Staking minimizes attacks by making it expensive to takeover a network (i.e. Sybil attacks) and causing an economic loss to anyone with negative intent on the network. Staking is done with a two-week waiting period to prevent users from quickly staking to liquidate their tokens.
“Our token model is similar to taxi medallions. You own Keep, you stake, and you can profit on being a privacy provider. Payments are a poor use case for tokens. In fact, most systems that use tokens for payment did so just to enable a fundraising mechanism. We don’t want it used for payments, because it’s a tax across the whole system against usage- and one of the coolest things tokens can do is let engineers build self-incentivizing systems that can grow themselves. What gives taxi medallions value is the ability to use them, in conjunction with your own effort, to make money,” explains co-founder Matt Luongo.
There are a million Keep tokens in total, half of which will be sold in the public and private sales.
The Keep Network
The Keep network uses keeps, or small units of private storage to securely encrypt and store private data.
There are two parties involved in the transmission of Keeps:
- Client – those who pay to use the keep’s storage capacity for secrets.
- Providers – those that hold the keep tokens and use them to compute and store secrets.
Keeps can be split across one or more providers. Anyone can run a keep provider, but these providers must put money on the line. These Keeps must be highly available, robust again data loss, and maintain both confidentiality and data integrity.
The Keep network includes a two main types of sMPC providers at the moment: simple and signing.
- Simple sMPC Keeps are backed by nodes. Each of these nodes has a part of the secret, but the secret can’t be revealed without collaboration from all of the nodes. The only way to do this is by Shamir secret sharing and encrypting each share with its respective node’s public key. Only then can the secret be published to the public blockchain or off-chain.
- Signing sMPC Keeps includes securing them with pseudorandom numbers and signing and encrypting the data. Signing Keeps can secure contracts on and off-chain. The randomization of the number generation is better than current methods on public blockchains, making it more secure.
There will be more providers developed in the future.
Both clients and providers are given incentives to prevent misbehavior on the network. While clients must purchase data storage on Keeps using the native token or Ether, providers are paid to use their computer power and storage by operating keeps. Each new Keep costs another security deposit. Providers receive payment for securely running Keeps over time and risk payments for misbehavior.
The Keep marketplace connects clients and providers together through a random selection process, called a random beacon, to ensure fairness. Members of the Keep network are placed into a threshold group. Each group has its own cryptographic signature. Each time a number is requested, a new group is chosen by the previous number and produces a cryptographic signature that creates the next random number. This method is called a threshold relay, because every new number generated is based on the previous number. The random beacon design was based on work developed by the Dfinity team.
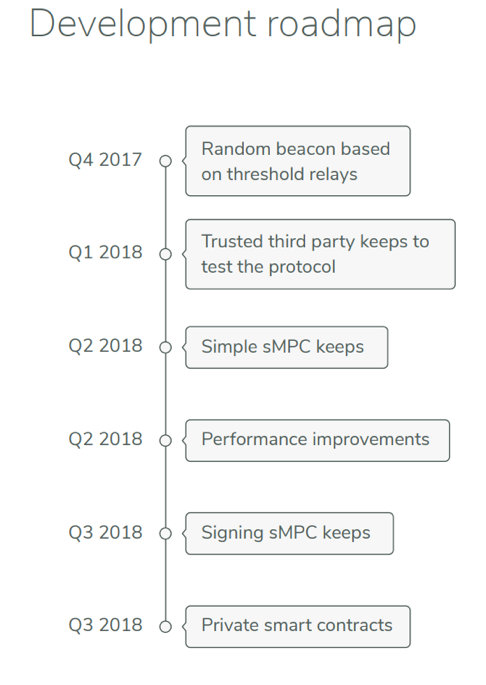
The ICO and Roadmap
Keep has not yet announced a token sale or air drop of any kind, but it is expected to occur in 2018. Keep’s fundraising goal for the token sale is $30 million. Participation in the ICO will be with Ethereum and Bitcoin.
In the meantime, the company has developed a Keep Guardian controlled programmatically to protect its community against phishing and scams leading up to the public sale. Keep plans to have the tokens available immediately after the public sale to ensure everyone who wants to can participate.
In Q3 of 2018 Keep plans to launch private smart contracts.